Smartphone Hacking: If you also keep a smartphone, then
this news is going to warn you. Actually, a cybersecurity company has asked
smartphone users to be careful. A cybersecurity company called Kaspersky Labs
has detected a virus, being told that the virus cannot be easily deleted.
With this virus, now around 250 crore smartphones
worldwide are under threat. The company said that this malware can always be
present in smartphones. By this, hackers can steal your personal data. This
vicious move of hackers has put the threat of more than 250 crore Android
smartphones all over the world.
Kaspersky Labs company has discovered this malware named
xHelper on the unofficial app marketplace. The company said that the hackers
cleverly use this malware to steal the data of users. It is being transported
in people's mobiles through a fake Cleaner app.
The most worrying thing is that this app hides after being
installed on the phone. You can see it neither on the home screen nor in the
program menu. You can see this dangerous app in the list of installed apps only
by going to Android system settings.
The company said in a post that it came to know about this
malware threat after checking the sample Trojan-Dropper.AndroidOS.Helper.h.
This malware is so dangerous that it accesses all the user's data after the backdoor
is installed. When the user tries to uninstall the app or malware, it is
automatically installed again.
According to experts, another malicious program is
installed in your phone with this malware, even after deleting it, reinstall
xHelper. However, cybersecurity experts have definitely suggested a way to
remove it from the phone. You have to set up recovery mode on your Android
phone. After this, you can replace the libc.so file with the original firmware
and replace it with the infected file.
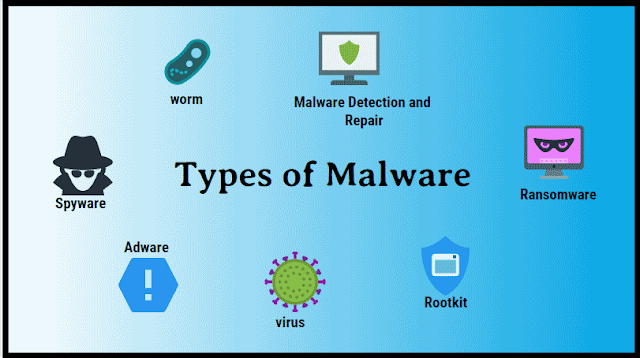
What is Malware
The term malware
is compression of malicious software. Simply put, malware is a piece of
software that was written with the intent of damaging devices, stealing data,
and generally causing disturbances. Viruses, Trojans, spyware, and ransomware
are among the different types of malware.
Malware is often
created by teams of hackers: usually, they are just looking to make money,
either by spreading the malware themselves or selling it to the highest bidder
on the Dark Web. However, there can be other reasons for creating malware - it
can be used as a tool for protest, a way to test security, or as a weapon of a war between governments.
Types of Malware:
1) Computer worm:
Worms also
prepare and spread their replication more actively than viruses based on other
files. Computer worms use removable media or networks to gain access to other
systems and typically require a program to assist them in this task. Worms that
spread through e-mail use the e-mail program of users to send themselves to all
the addresses in the address book. Like viruses, Worms can damage systems and
are often used to gain covert control over computers. Worms are considered the
most common type of malicious software.
2) Computer viruses:
Viruses are
programs that are capable of spreading differently by making copies of
themselves and then infiltrating other computer programs. A virus is the best known and oldest type of malware. A virus multiplies after the virus program
starts, and then interferes with the computer's functions, spying on users,
destroying data, or even damaging the hardware.
3) Trojan horse:
Trojan horse is a
type of malware that initially pretends to be a useful and secure application
so that it can access a computer's system. It performs functions that are
mostly hidden from users. Trojan horses can carry out many harmful actions such
as monitoring the data traffic of a computer. Some of these actions take place
with the copying and sending of information or files, while others execute
special tasks on the computer in addition to replacing or installing new
software. It is also possible to remotely control Trojan horses through a
backdoor function, which allows other users the opportunity to hijack the
computer for cybercriminal purposes.
4) Adware:
The term adware
is considered to be a contraction of advertisement and software and is operated
by placing advertisements in the program. It is usually included in free
software and is mostly legitimate, but it can also be dangerous if it shows a
pop-up or fake website, or makes any changes to the system or browser settings
without permission.
5) Spyware:
This type of
malware is used to uncover user data and send it to the manufacturer or a third
party. Even when Spyware comes into the PC, the user is completely unaware that
their behavior is being recorded. The information obtained by spyware is mostly
analyzed for commercial purposes to show customized advertisements for example.
6) Ransomware:
The software goes
one step ahead of the software by blocking access to the computer's operating
system or blocking critical files. This program demands payment of a ransom to
withdraw the blocked data.
7) Scareware:
This malware
focuses on scaring and harassing users by displaying fake warnings about
malware discovered on computers. If an advertisement for fee-based software
appears in a pop-up on your PC that claims to be able to remove your PC's
alleged malware, it is known as rogue security software or rogueware. If the
user buys this allegedly useful application and installs it, then a lot of
malware will usually appear on the computer.
8) Backdoor:
Backdoor is also
known as a trapdoor. It is a function rather than an independent program. A part
of the software is known as a backdoor when an external user succeeds in accessing
the computer. This happens without the knowledge of the users. Often, remort
access is used to perform service-related attacks, which occur when Internet
services perlize or send spam e-mail. Backdoors can be installed by Trojan
horses, viruses, or worms.
April 27, 2020
Tags :
Hacking
,
Virus
Subscribe by Email
Follow Updates Articles from This Blog via Email


No Comments